From initial triage through structured export, Intreys™ covers the full investigation lifecycle.
🔎
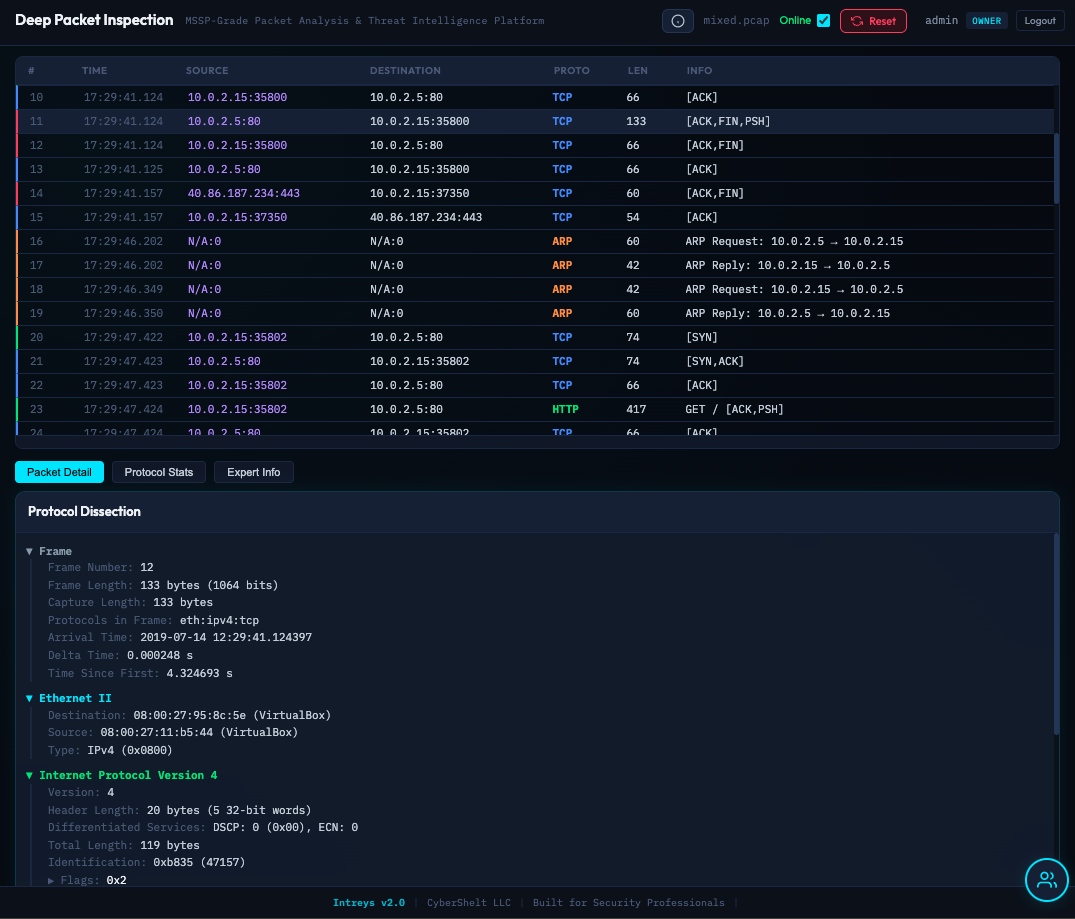
Deep Packet Inspection
Wireshark-compatible display filters, full TCP/UDP stream reassembly, hex dump inspection, protocol tree dissection, and expert info panels. Virtual scrolling handles 500K+ packet lists.
🎯
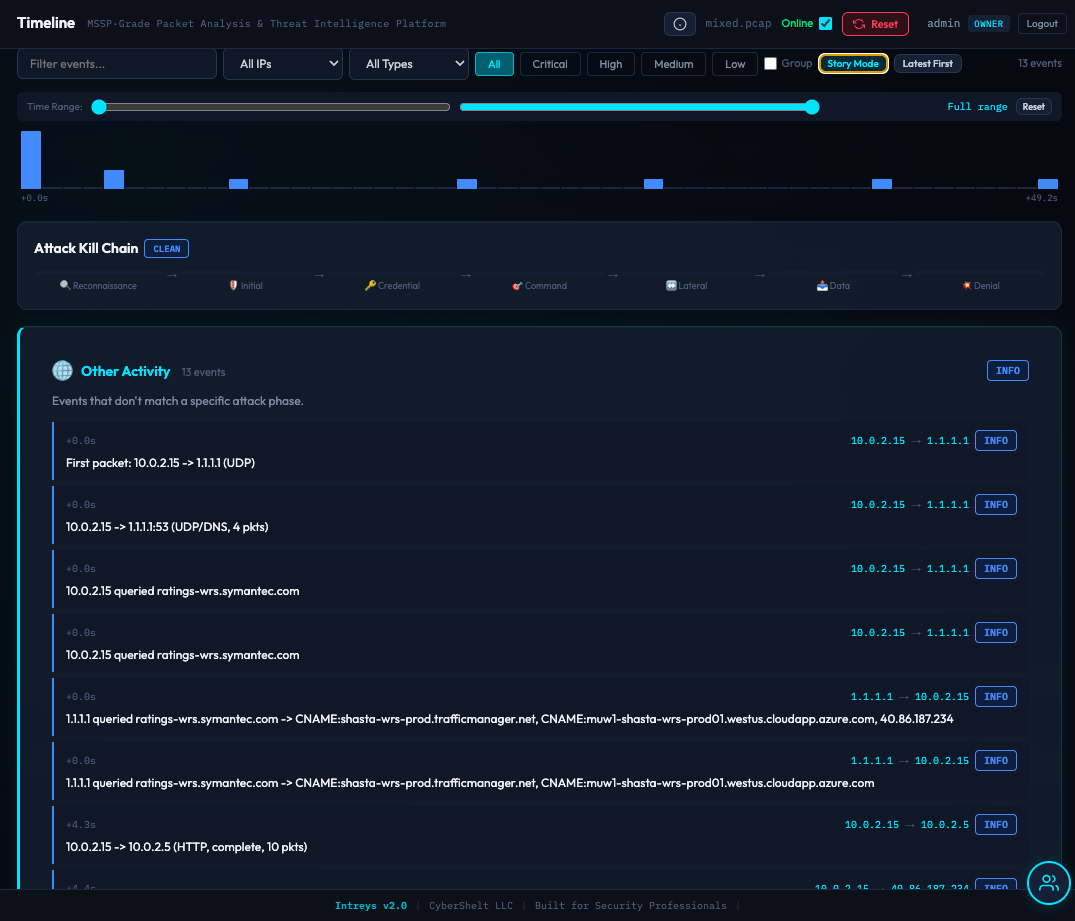
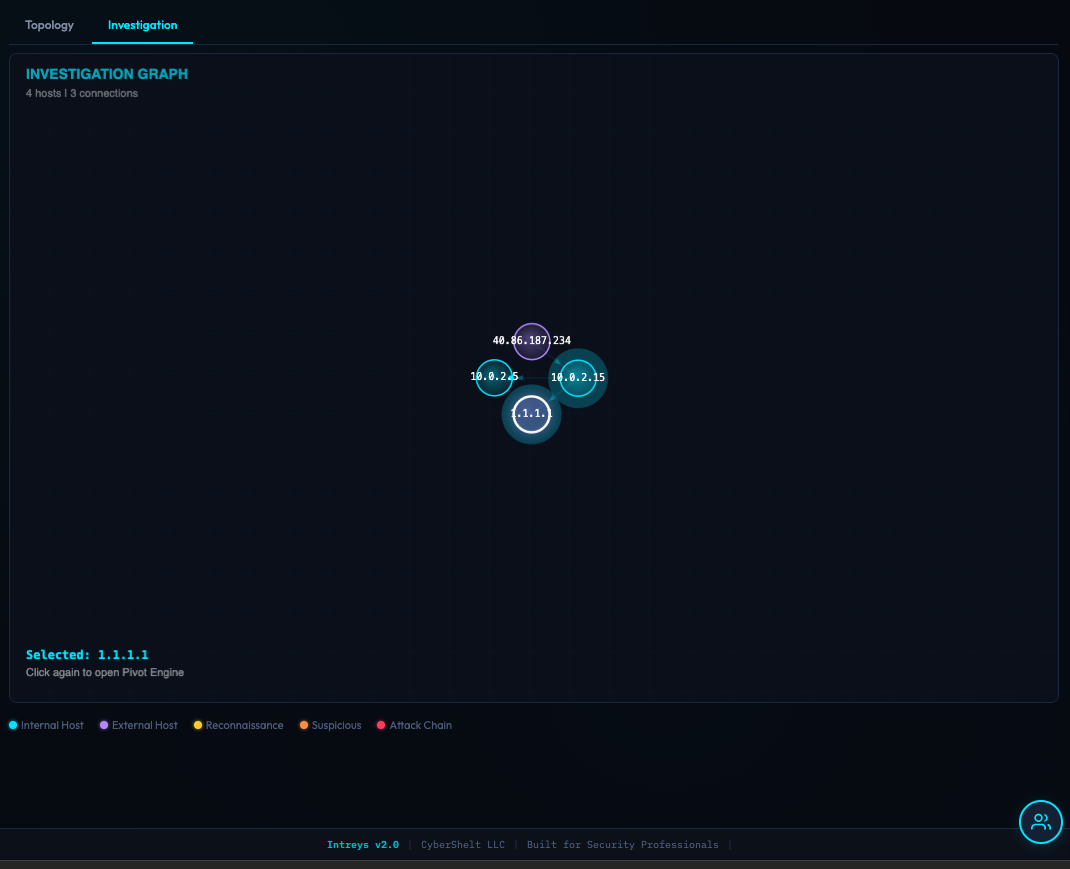
Automated Threat Hunting
C2 beacon detection, DNS tunneling, data exfiltration, lateral movement, port scanning, credential theft, and covert channel analysis. Hypothesis-driven hunts with playbook-guided investigation.
🤖
AI-Assisted Analysis
Attack narrative generation with Mermaid diagrams. Local AI analysis (runs on your hardware). Cloud providers supported with privacy controls and cost tracking.
🏭
ICS/SCADA Security
10 industrial protocol dissectors including Modbus, DNP3, S7comm, IEC-104, and OPC UA. Security policy enforcement, dangerous operation detection, and per-host health scoring.
📡
Live Packet Capture
High-performance capture engine with real-time streaming. PCAP file writing for captured traffic. No external tools required.
📈
MITRE ATT&CK Mapping
Visual ATT&CK matrix with detected techniques. Pyramid of Pain indicator classification. ATT&CK Navigator JSON export for team collaboration.
📦
Export Everywhere
STIX 2.1, MISP, TAXII 2.1, Sigma rules. PDF and DOCX reports. Full JSON and CSV export. YARA rule scanning on extracted artifacts.
🔒
Enterprise Security
Role-based access control, encrypted API key storage, login rate limiting, enterprise-grade security controls, audit logging, and cryptographically signed license verification.
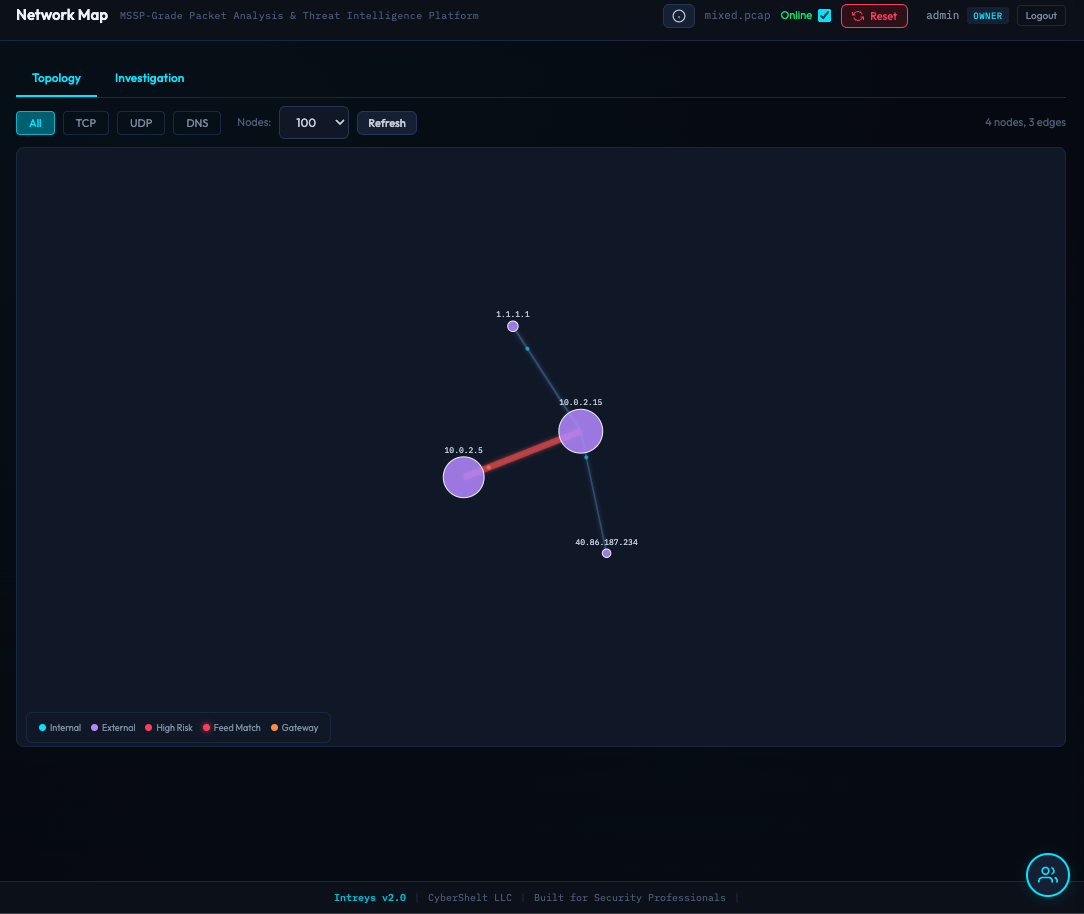
🌐
Threat Intelligence
Online enrichment via AbuseIPDB, VirusTotal, GreyNoise, OTX, Shodan, and URLScan. Threat feed ingestion with local caching for offline use. DGA detection.